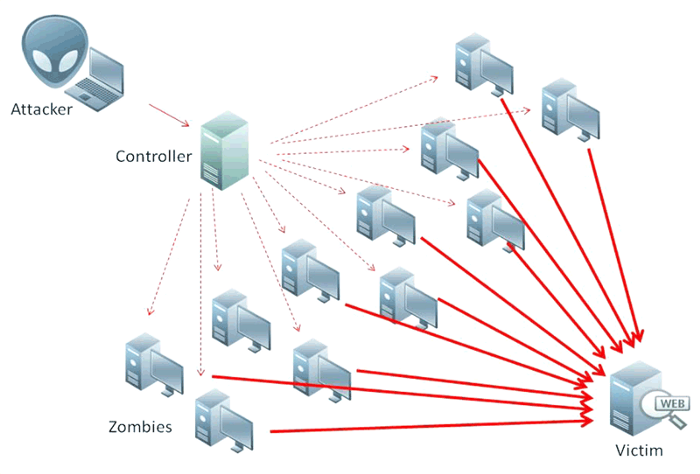
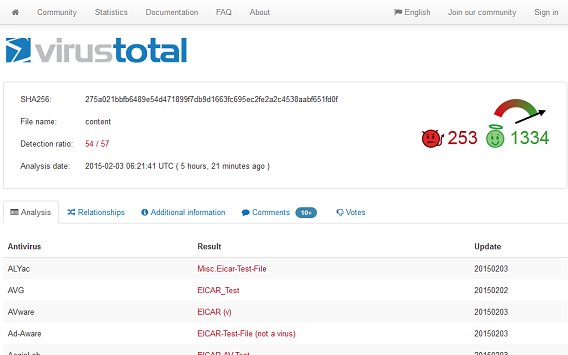
A DDoS attack is an attack that targets a website. It works by flooding the target website with bogus traffic. By doing this, the attackers are able to “flood” and disrupt the service. This makes it unavailable for legitimate users. The impact of such an attack can be significant. It can lead to prolonged downtime, lost revenue, and dissatisfied customers.
The most important step in dealing with DDoS is to be prepared. This is what you do BEFORE the attack is launched. Identify the potential targets: assets, including servers, applications, and services. Then, you need to determine what effect the outage will have on your customers and users. The cost of an outage is your justification for budgets to fund your countermeasures. Create an incident response playbook.
Preparation Step 1
Have you done capacity planning? How many concurrent visitors can your existing setup handle? Would it make sense to add more memory, CPUs, bandwidth and faster SSD to your storage? Have you optimized your current code so that more visitors can be served? Do you have SNMP monitoring and alerts? Did you enable firewall, web and event logging? It is also important to set up security policies to protect sensitive data. Are all your systems fully updated and patched?
Preparation Step 2
Have you hardened your defenses yet? Did you update your rules for Intrusion protection and detection systems? These are your first line of defense. The attacks that gets past your first line of defense can be stopped by a second line. This is your Web Application Firewall (WAF/modsec). The combination usually is enough to filter out a lot of unwanted traffic.
The key point is to filter out unwanted traffic. You need to create a filter that allows legitimate traffic and discards illegitimate traffic. But understand that it is still no defense against a flood of traffic that is 100X what the server is setup to handle.
Preparation Step 3
Notice that hackers concentrate their DDoS ‘firepower’ onto a target. You can force hackers to spread out their attacks by adding more webservers. You can use Content distribution Networks — CDNs Like CloudFlare, Google’s Project Shield, AWS Shield, Akamai to name but a few.
These CDNs not only provide more bandwidth but also diffuse the DDoS’ impact. The attacks are now spread across several locations. This is like the classic Colonel Blotto Game. It boils down to a matter of forcing your opponents to commit more resources. You do this by opening more ‘fronts’ in the battlefield. The CDN is one way to force the DDoS to attack multiple fronts — instead of just one.
Preparation Step 4
Have you considered a paradigm shift? An out of the box solution should consider the power of distributed web. Rather than a single source of web files, think of using a bit torrent like solution, where the web files sit on multitudes of PCs. The CDN killer app is Brave (browser) + IPFS.
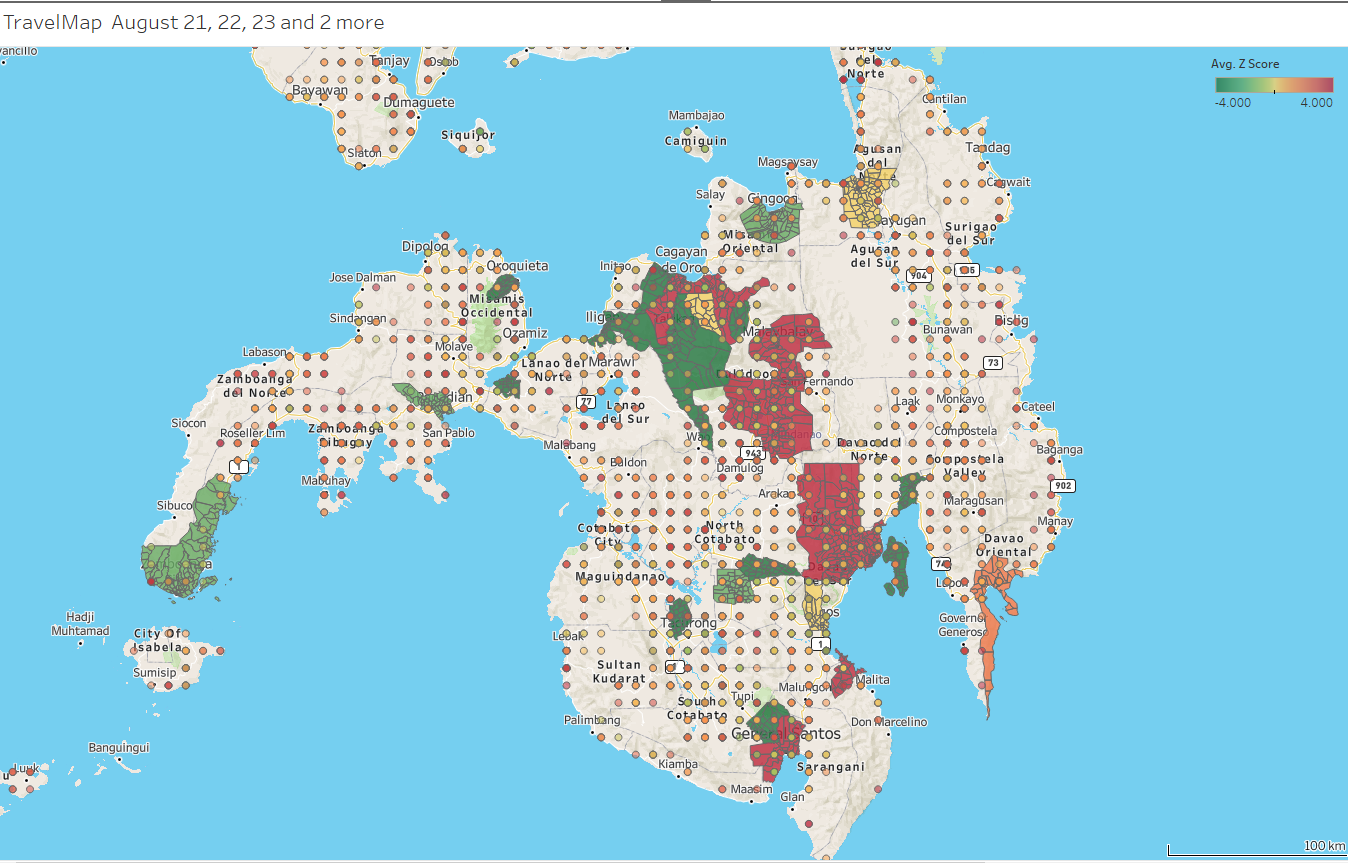
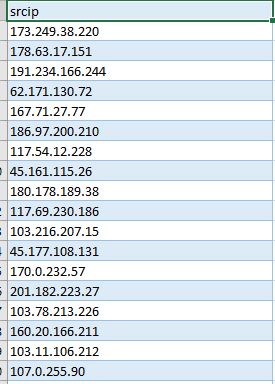
You need to quickly identify the source of the problem. Your SNMP Monitoring can quickly zero in on the asset/s being attacked. You need to notify your customers as soon as you notice that they’re being attacked. It’s important that everyone is aware of the potential risk.
Your web and firewall log files come in handy to identify the assets that are impacted. You can use this data to see whether your customers are seeing a difference in service quality. Find out the Who, When, How of the attacks. And then respond accordingly.
Post Mortem
Hold a “Lessons Learned” after the attack and update your incident response playbook. How can your response teams react faster? Got more to add? Please share your thoughts.